Byte-Sized Lesson: Troubleshooting Study
During the last two years, the primary purpose of this series of Byte-Sized Lessons was to assist the AV industry in understanding TCP/IP technology. We’ve discussed and examined protocols, addressing, standards, and how IP is used. This article will present a case study and give you the opportunity to apply what these lessons have shown.
SITUATION
Abigail works for XYZ Company as a video technician. She installs cameras, encoders, decoders, digital signage, DVRs, and similar AV devices. Recently, the company consolidated two offices and she inherited a camera from the one that was closed. She would like to redeploy it in her network. She knows the office that closed used the subnet address 192.168.18.0/24 and she is confident that the password shared by all the company cameras is the same. She can use the Ethernet/web interface to the camera but must know the current IP address that has been assigned to it. Unfortunately, the technician who knows the address left the company when the office closed. How can she get the address? I suggest you pause to think about a possible method and then read further.
POSSIBLE SOLUTIONS
Some people would quickly respond, “Do a factory reset and start over.” However, there is a disadvantage to that method. Even if it can be done, after the reset, all firmware upgrades will need to be reinstalled, which could be time consuming.
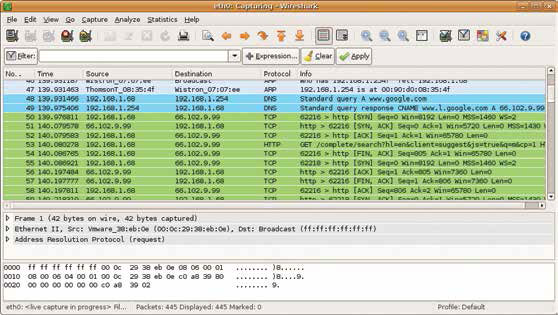
Most IT technicians would immediately think of using the free software utility Wireshark. With it, you can see and record all packets on a network. By connecting it to the camera, you can analyze how it attempts to join the network.
Turning now to the camera: when it boots, it will follow a procedure much as any network-attached computing device would. Let’s say the camera is configured with the address 192.168.18.22. One of the first things the camera will likely do when it is powered on is to determine if that address is already in use. So, it will send an ARP (address resolution protocol) packet as a broadcast, which asks, “Does anyone have the address 192.168.18.22? Tell my mac address about it.” If Abigail has Wireshark connected to the camera and running, she’ll see this exchange.
A daily selection of features, industry news, and analysis for tech managers. Sign up below.
Suppose the camera doesn’t usually check for duplicated addresses. It is still very likely that it will attempt to connect to its local router (gateway). If the camera is configured in the typical manner, its router will be 192.168.18.1. Again, when the camera is powered on, Abigail can use Wireshark to see the ARP packet asking, “Who has the address 192.168.18.1? Tell 192.168.18.22.” With the IP address and the password, she can now reconfigure the camera for her own network.
This process is simple and should take no more than five minutes. If you are responsible for device support and maintenance, Wireshark is an excellent tool to have installed on you PC.
Phil Hippenstel, PhD, is a regular columnist with AV Technology. He teaches information systems at Penn State Harrisburg.